Volume Shadow Copy (also known as Volume Snapshot Service or VSS ) is a technology included in Microsoft Windows. It allows the ability to take backup copies or snapshots of computer files or volumes whether in use or not. The process can be operated manually or automatically.
Can be used to view read only snapshot points in time.
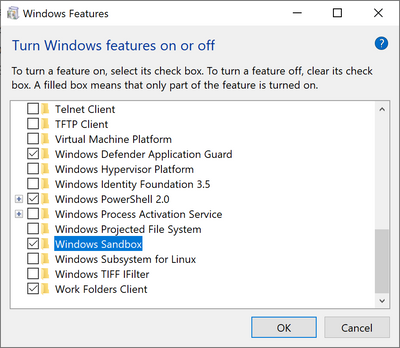
How to turn on Volume Shadow Copies:
- Type restore in the windows search menu
- Select create restore point
3. Select Configure
4. Turn on system protection

5. Create is enabled as an option and name it
 |
| Success |
CURRENT STICKY NOTE
USING VOLUME SHADOW COPIES TO VIEW RESTORED STICKY NOTES
Opening a CMD prompt with admin privileges
Typing "vssadmin list shadows"
Using the Shadow Copy Volume field for the make link command
Typing "mklink /d outputvolume \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy1\" *including the trailing back slash at the end of the Shadow Copy Volume name
mklink command /d <source><destination>
 |
| Linked Volume is now there |
PATHING TO THE "plum.sqlite" file related to Sticky Notes
"Users\<Username>\AppData\Local\Packages\Microsoft.MicrosoftStickyNotes_8wekyb3d8bbwe\LocalState"

Using DB Browser to view SQLITE file
dowload from site: https://sqlitebrowser.org/dl/
After copying the
plite file to the another directory out of the mklinked directory, can
open and view the deleted entry that was saved in the restored point shadow
copy.
*Can also run strings on "plum.sqlite-wal" in the LocalState folder from the VS copy
strings .\plum.sqlite-wal
--Bryan