From the Windows Local Group Policy Editor, details of policy:
At least Microsoft Windows 7 or Windows Server 2008 family.
"This policy setting lets you capture the input and output of Windows PowerShell commands into text-based transcripts.
If you enable this policy setting, Windows PowerShell will enable transcripting for Windows PowerShell, the Windows PowerShell ISE, and any other applications that leverage the Windows PowerShell engine.
By default, Windows PowerShell will record transcript output to each users' My Documents directory, with a file name that includes 'PowerShell_transcript', along with the computer name and time started.
Enabling this policy is equivalent to calling the Start-Transcript cmdlet on each Windows PowerShell session.
If you disable this policy setting, transcripting of PowerShell-based applications is disabled by default, although transcripting can still be enabled through the Start-Transcript cmdlet.
If you use the OutputDirectory setting to enable transcript logging to a shared location, be sure to limit access to that directory to prevent users from viewing the transcripts of other users or computers.
Note: This policy setting exists under both Computer Configuration and User Configuration in the Group Policy Editor. The Computer Configuration policy setting takes precedence over the User Configuration policy setting."
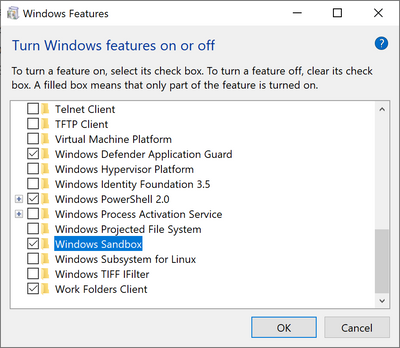
1. Windows key run --> gpedit.msc
2. Navigate to:
Computer Configuration –
Administrative Templates – Windows Components – Windows PowerShell and double-klick “Turn on PowerShell Transcription”.
Click on Enable and enter your preferred Output Directory. (include invocation
headers will log the PS command start time)
 |
| The transcript was manually picked to be at C:\PS_Transcripts. Can output to anywhere, for instance a share server or log server. |
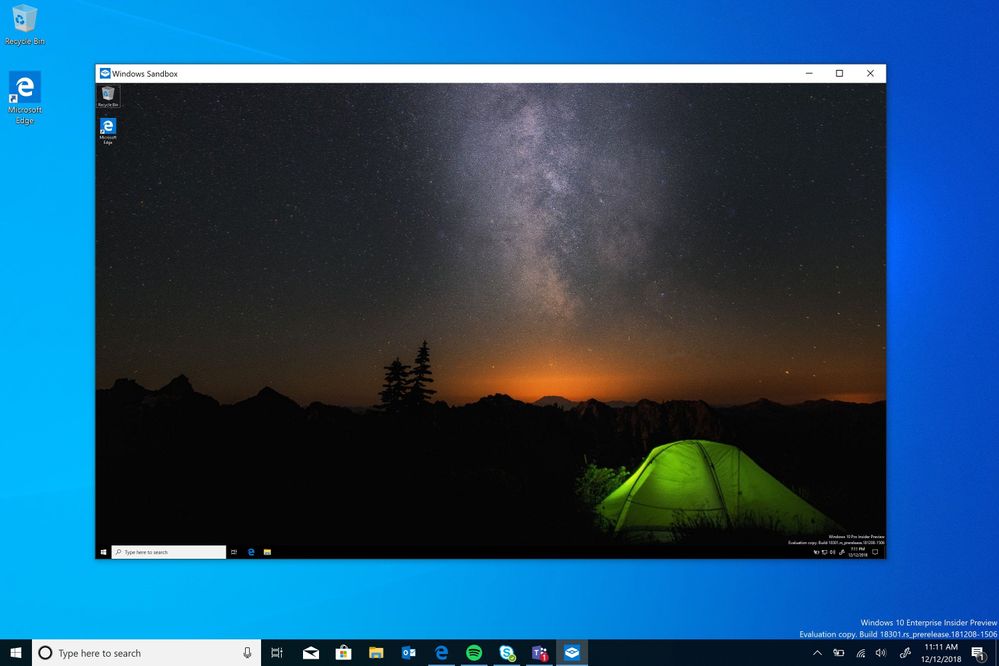
3. The transcript file will now be created in the selected output directory
 |
| Above is the PS transcript with the starttime, username, host, and scripts that was ran, with output |
--Bryan